Researchers at security company Proofpoint and PricewaterhouseCoopers (PWC) said on Tuesday they had identified a cyber espionage campaign that delivers the ScanBox exploitation framework through a malicious fake Australian news site.
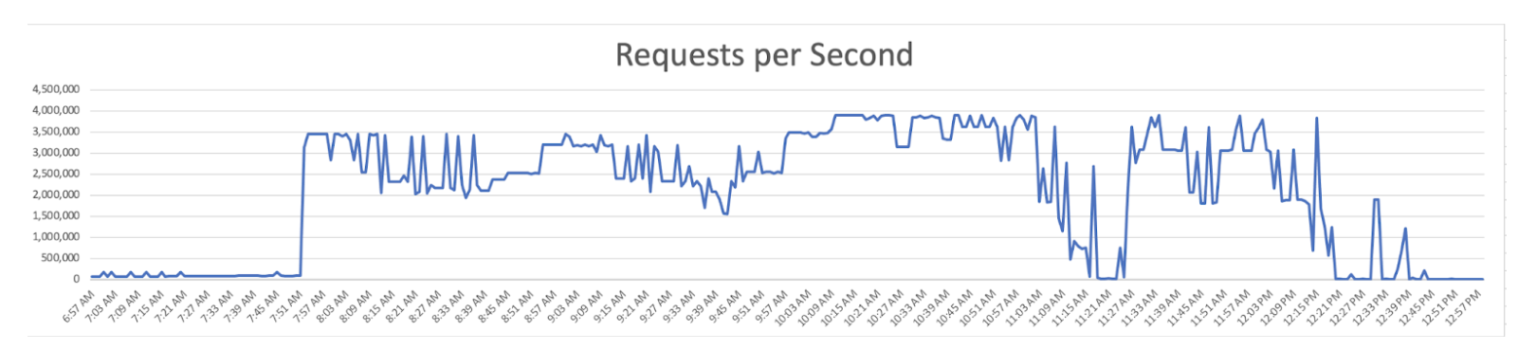
The campaign, active from April to June of this year, targeted Australian government agencies, Australian media companies and manufacturers who conduct maintenance on wind turbine fleets in the South China Sea. Proofpoint said the victim profile was similar to a June 2021 TA423 threat that delivered a downloader in DLL format via RTF template injection.
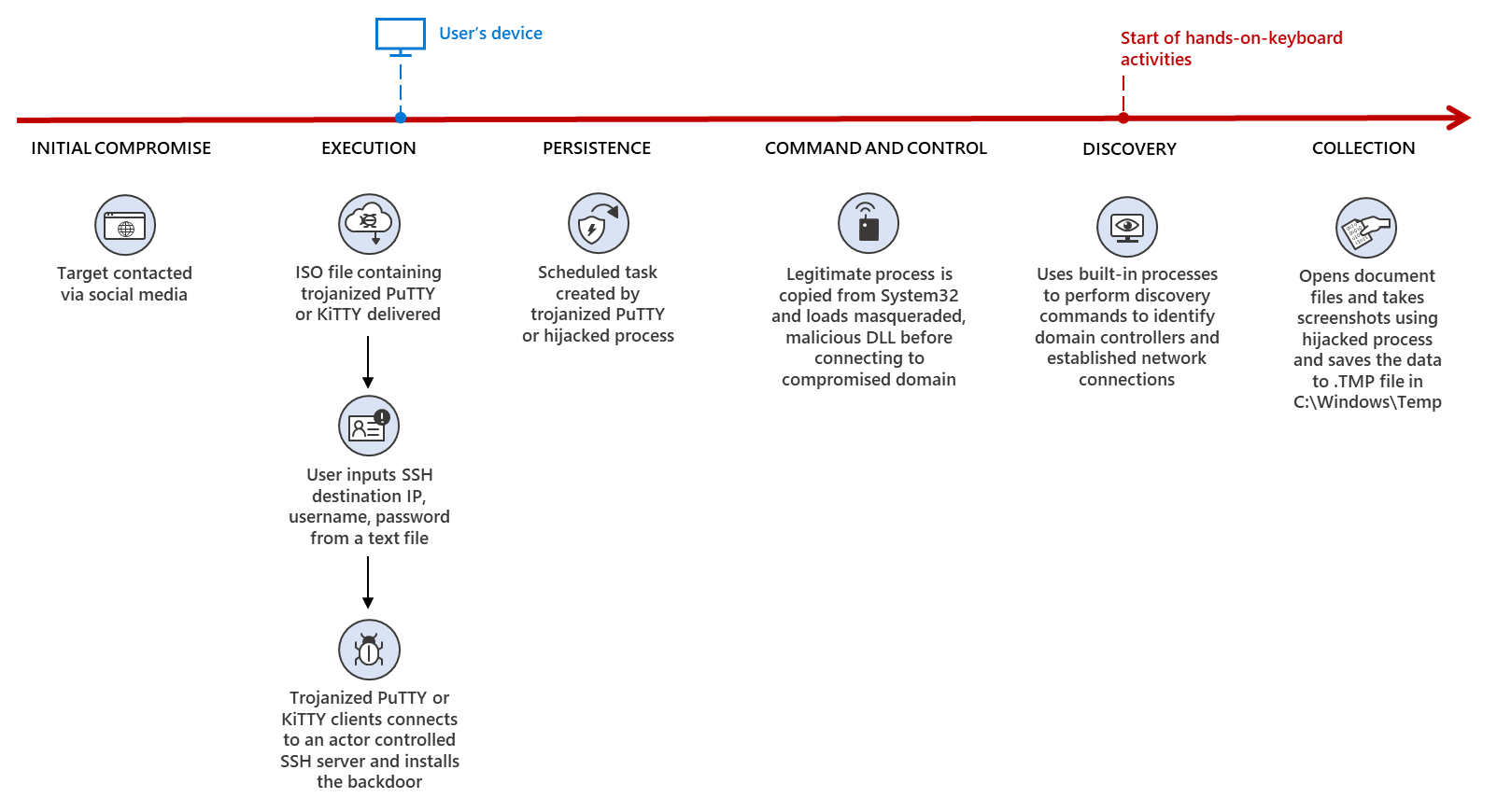
According to the researchers, victims were sent phishing emails that directed them to faked versions of Australian news outlets The Herald Sun and The Australian. Both outlets are part of Rupert Murdoch's media empire.
The faked versions of the outlets' sites included copied and pasted news stories, but lurking deeper in the code was malware. This tactic is similar to one used by TA423 during 2018 elections in Cambodia.
Each target received a slightly different URL that led to the same page, indicating the threat actors may have tracked its victims rather than use a spray and pray method.
Once lured to the site, users were infected with a malicious ScanBox JavaScript payload as a plugin-based modular architecture. The plugin modules included a keylogger, browser identification plugins, browser fingerprints to identify system tech capabilities, peer connection plugins and a check if Kaspersky security tools are installed on the machine.

China-linked APT40 targets wind turbines, Aust. government
ScanBox installed after victims lured to fake Murdoch news sites with phishing emails