Install the app
How to install the app on iOS
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
ELSO (elektroninen sodankäynti) radiotaajuuksilla: radiotiedustelu, taajuushäirintä, EMP etc
- Viestiketjun aloittaja Pyllyvaltteri
- Aloitus PVM
Suluttaja
Kapteeni
Dave Tremper, director of electronic warfare for the Office of the Secretary of Defense, pointed to SpaceX’s ability last month to swiftly stymie a Russian effort to jam its Starlink satellite broadband service, which was keeping Ukraine connected to the Internet. SpaceX founder Elon Musk steered thousands of Starlink terminals to Ukraine after an official sent him a tweet asking for help keeping the besieged country online.
“The next day [after reports about the Russian jamming effort hit the media], Starlink had slung a line of code and fixed it,” Tremper said. “And suddenly that [Russian jamming attack] was not effective anymore. From [the] EW technologist’s perspective, that is fantastic … and how they did that was eye-watering to me.”
The government, on the other hand, has a “significant timeline to make those types of corrections” as it muddles through analyses of what happened, decides how to fix it and gets a contract in place for the fix.
“We need to be able to have that agility,” Tremper said. “We need to be able to change our electromagnetic posture to be able to change, very dynamically, what we’re trying to do without losing capability along the way.”
Redundancy is also critical so the U.S. could keep operating on another system if an EW attack succeeded at knocking one out, Tremper said.
The U.S. needs to think a lot more innovatively when it comes to building new EW equipment, Clark said. It won’t be enough to just buy upgraded versions of legacy systems, he said — the U.S. has to come up with new systems that allow for much greater resilience and speed.
This includes incorporating artificial intelligence and machine learning into next-generation systems to be able to respond faster, he said. Increased use of digital engineering can also help the military model new equipment with a computer and work out the kinks before going through the time-consuming typical acquisition and testing process.
Clark said the Air Force’s in-development Compass Call, the EC-37B, is a prime example of how digital engineering is transforming how the service approaches new electromagnetic warfare capabilities.
Software coders and engineers are working with Compass Call operators on the ground to figure out creative ways to jam enemy signals, Clark said.
Russia’s invasion of Ukraine has taught the U.S. a great deal about the sophistication and reliability of Russian equipment, they said, and their troops’ ability to carry out missions in a synchronized way.
In particular, Tremper said, it has shown how important it is to properly train the personnel assigned to carry out electromagnetic warfare operations. Trying to carry out EW while moving forward inside the territory you’re invading, and not in a secure location, makes it even trickier.
“It’s a very hard problem, if you don’t have well-trained operators,” Tremper said. “The degree of coordination and synchronization of these types of operations is such that the undertrained operator will have a harder time pulling off those types of events successfully.”
Tremper said the Pentagon expected a “much stronger” EW showing from Russia — but cautioned that isn’t to say all of Russia’s efforts have failed.

SpaceX shut down a Russian electromagnetic warfare attack in Ukraine last month — and the Pentagon is taking notes
“The next day, Starlink had slung a line of code and fixed it," said Pentagon electronic warfare director Dave Tremper. "And how they did that was eye-watering to me."
US Navyn ECM-koulutusvideo vuodelta 1962.
Todella mielenkiintoinen puolituntinen elsosta kiinnostuneelle, mutta siitä vähän tietävälle tai vähän ymmärtävälle. Video on rautalankaintro aiheeseen, joka pyrkii kertomaan miten EW toimii eri uhkia vastaan. Hämmästyttävän monimutkaisia EW-ratkaisuja oli jo tuon aikakauden koneissa, voi vain kuvitella niiden kompleksisuuden nyt 60 vuotta myöhemmin!!
Videossa avattiin kevyesti myös tehtävätaktiikkaa ja -suunnittelua. Siinä korostetaan (signaali)tiedustelun roolia. Tunnistamalla vastassa olevat kohteet ja niiden sijainteja voidaan myös EW-suojan käyttö optimoida tehtävää varten.
Todella mielenkiintoinen puolituntinen elsosta kiinnostuneelle, mutta siitä vähän tietävälle tai vähän ymmärtävälle. Video on rautalankaintro aiheeseen, joka pyrkii kertomaan miten EW toimii eri uhkia vastaan. Hämmästyttävän monimutkaisia EW-ratkaisuja oli jo tuon aikakauden koneissa, voi vain kuvitella niiden kompleksisuuden nyt 60 vuotta myöhemmin!!
Videossa avattiin kevyesti myös tehtävätaktiikkaa ja -suunnittelua. Siinä korostetaan (signaali)tiedustelun roolia. Tunnistamalla vastassa olevat kohteet ja niiden sijainteja voidaan myös EW-suojan käyttö optimoida tehtävää varten.
Laitan tänne,
 spectrum.ieee.org
spectrum.ieee.org
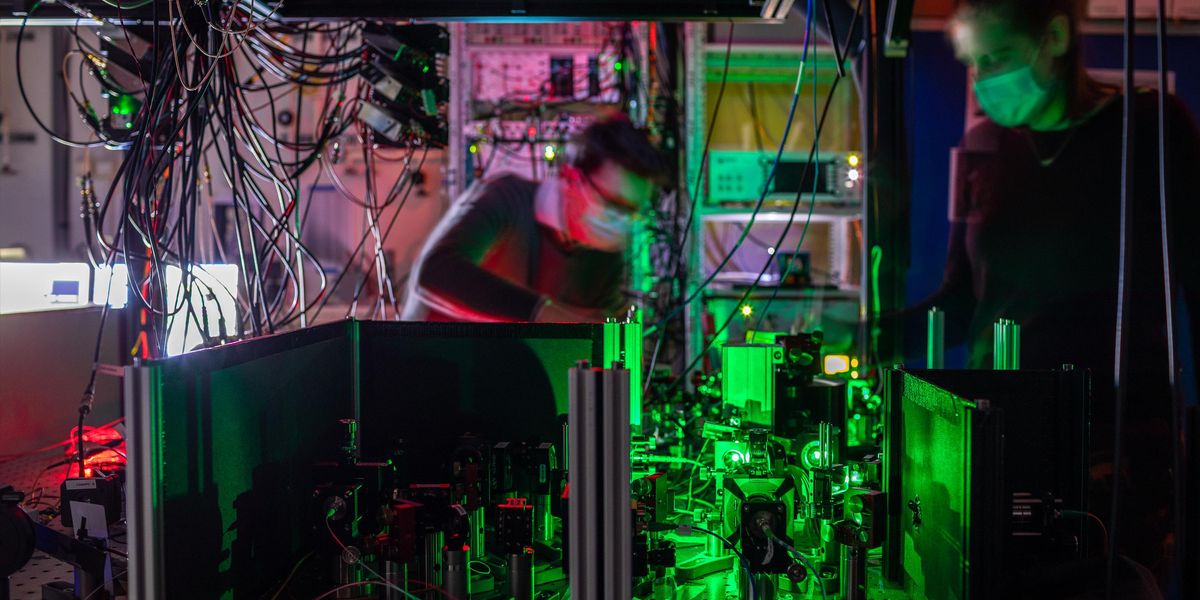
En keksi mitään keinoa jolla pystyy kuuntelemaan quantum teleportattua infoa.
Since quantum teleportation first became a reality 25 years ago, scientists have pushed its limits. Teleportation—outside the Star Trek universe—consists of transmitting a quantum state from one system to another via quantum entanglement. The two quantum systems (two atoms in a laser trap) can be right next to one another, or they can be separated by arbitrarily large distances. Strange as it sounds, quantum teleportation has been widely observed in the lab and even harnessed in emerging quantum technologies. To date, scientists have achieved quantum teleportation across distances as great as 1,400 kilometers. Yet there are other kinds of limitations than physical distance. Until now, quantum teleportation could only happen between, say, atoms that had been in direct contact with each other.
But in a new study, researchers have for the first time accomplished quantum teleportation between two remote nodes that share no direct connection whatsoever. This advance represents an important step toward a quantum Internet that would connect quantum computers together—enabling them to share data and computations a little as today’s cloud-computing frameworks do for classical computers.
Expanding Horizons of Long-Haul Quantum Communications
In a new study, researchers have for the first time accomplished quantum teleportation between two remote nodes that share no direct connection whatsoever. This advance represents an important step toward a quantum Internet that would connect quantum computers together.
 spectrum.ieee.org
spectrum.ieee.org
To develop a quantum Internet that can link quantum computers together and transmit quantum-encrypted messages, scientists need a way to share quantum information between the nodes of the network. However, such quantum data is fragile. If you wanted to send quantum information encoded in photons, quantum data loss would inevitably happen over great enough lengths of glass fibers.
A potentially better way to send quantum information across large distances is via quantum teleportation. Just like in science fiction, quantum data that undergoes such teleportation essentially disappears one place and reappears someplace else. Since this quantum information does not travel across the intervening space, there is no chance it will get lost.
In the new study, researchers experimented with three nodes, dubbed Alice, Bob and Charlie. They successfully performed quantum teleportation between Charlie to Alice, with the help of intermediate node Bob. This is the first time quantum teleportation was accomplished between two nodes that were not adjacent to one another.
Each node consisted of a microscopic artificial diamond with a defect within it, in which a carbon atom is replaced with a nitrogen atom and the adjacent carbon atom is missing. The spin of single electrons trapped in these “nitrogen-vacancy centers” can encode quantum data as a quantum bit, or qubit.
Optical fibers connected the nodes. Direct links existed between Alice and Bob and between Bob and Charlie, but not between Alice and Charlie. The researchers used these links to set up entanglement between Alice and Bob and between Bob and Charlie.
In addition, in each of Bob and Charlie’s diamonds, a carbon-13 atom served as a “memory qubit.” These memory qubits let these nodes store and then swap their entanglement data, resulting in Alice becoming entangled with Charlie. This enabled the scientists to finally teleport data from Charlie to Alice.
En keksi mitään keinoa jolla pystyy kuuntelemaan quantum teleportattua infoa.
Since 2018, Elon Musk’s Starlink has launched more than 3,000 small satellites into orbit. This satellite network beams internet connections to hard-to-reach locations on Earth and has been a vital source of connectivity during Russia’s war in Ukraine. Thousands more satellites are planned for launch as the industry booms. Now, like any emerging technology, those satellite components are being hacked.
Today, Lennert Wouters, a security researcher at the Belgian university KU Leuven, will reveal one of the first security breakdowns of Starlink’s user terminals, the satellite dishes (dubbed Dishy McFlatface) that are positioned on people’s homes and buildings. At the Black Hat security conference in Las Vegas, Wouters will detail how a series of hardware vulnerabilities allow attackers to access the Starlink system and run custom code on the devices.
To access the satellite dish’s software, Wouters physically stripped down a dish he purchased and created a custom hacking tool that can be attached to the Starlink dish. The hacking tool, a custom circuit board known as a modchip, uses off-the-shelf parts that cost around $25. Once attached to the Starlink dish, the homemade printed circuit board (PCB) is able to launch a fault injection attack—temporarily shorting the system—to help bypass Starlink’s security protections. This “glitch” allows Wouters to get into previously locked parts of the Starlink system.

The Hacking of Starlink Terminals Has Begun
It cost a researcher only $25 worth of parts to create a tool that allows custom code to run on the satellite dishes.
Wouters is now making his hacking tool open source on GitHub, including some of the details needed to launch the attack. “As an attacker, let’s say you wanted to attack the satellite itself,” Wouters explains, “You could try to build your own system that allows you to talk to the satellite, but that’s quite difficult. So if you want to attack the satellites, you would like to go through the user terminal as that likely makes your life easier.”
The researcher notified Starlink of the flaws last year and the company paid Wouters through its bug bounty scheme for identifying the vulnerabilities. Wouters says that while SpaceX has issued an update to make the attack harder (he changed the modchip in response), the underlying issue can’t be fixed unless the company creates a new version of the main chip. All existing user terminals are vulnerable, Wouters says.
Starlink says it plans to release a “public update” following Wouters’ presentation at Black Hat this afternoon, but declined to share any details about that update with WIRED prior to publication.
“If you’re trying to tell whether you’re being followed, there are surveillance detection routes,” Edmondson says. If you’re driving, you can change lanes on a freeway, perform a U-turn, or change your route. Each can help determine whether a car is following you. But it didn’t feel like enough, Edmondson says. “He had those skills, but he was just looking for an electronic supplement,” Edmondson explains. “He was worried about the safety of the confidential informant.”
After not finding any existing tools that could help, Edmondson, a hacker and digital forensics expert, decided to build his own anti-tracking tool. The Raspberry Pi-powered system, which can be carried around or sit in a car, scans for nearby devices and alerts you if the same phone is detected multiple times within the past 20 minutes. In theory it can alert you if a car is tailing you.
The device runs Kismet, which is a wireless network detector, and is able to detect smartphones and tablets around it that are looking for Wi-Fi or Bluetooth connections. The phones we use are constantly looking for wireless networks around them, including networks they’ve connected to before as well as new networks.
Edmondson says Kismet makes a record of the first time it sees a device and then the most recent time it was detected. But to make the anti-tracking system work, he had to write code in Python to create lists of what Kismet detects over time. There are lists for devices spotted in the past five to 10 minutes, 10 to 15 minutes, and 15 to 20 minutes. If a device appears twice, an alert flashes up on the screen. The system can show a phone’s MAC address, although this is not much use if it’s been randomized. It can also record the names of Wi-Fi networks that devices around it are looking for—a phone that’s trying to connect to a Wi-Fi network called Langley may give some clues about its owner. “If you have a device on you, I should see it,” he says. In an example, he showed WIRED that a device was looking for a network called SAMSUNGSMART.
To stop the system from detecting your own phone or those of other people traveling with you, it has an “ignore” list. By tapping one of the device’s onscreen buttons, it’s possible to “ignore everything that it has already seen.”

This Anti-Tracking Tool Checks If You’re Being Followed
The Raspberry Pi-powered device can scan for phones around you. If it keeps spotting the same one, it’ll send you an alert.
GitHub - azmatt/chasing_your_tail: Tool for using wireless signals to see if you're being followed.
Tool for using wireless signals to see if you're being followed. - GitHub - azmatt/chasing_your_tail: Tool for using wireless signals to see if you're being followed.
A security researcher has shown how to, with physical access at least, fully take over a Starlink satellite terminal using a homemade modchip.
Lennert Wouters, a researcher at the KU Leuven University in Belgium, walked through his methodology during a talk at Black Hat in Las Vegas this week.
Wouters said he will release the code and details of components used via GitHub so other folks can build their own modchips that when fitted to the SpaceX hardware unlock the broadband satellite equipment. This will allow them to poke around for additional security holes in the device and possibly the network, play with the configuration, and discover any other functionality.

Starlink satellite dish cracked on stage at Black Hat
Once the modchip plans are live, you can, too
Developing the modchip took "a significant amount of time" over the better part of a year, according to Wouters.
First, he compromised the black-box system using voltage fault injection during the execution of the system-on-chip ROM bootloader, which allowed him to bypass the firmware signature verification and run his own custom code on the terminal. This was all done in a lab setting, with various electronics to help, so don't think this could be used against, say, a dish at a stranger's home, Wouters said.
After successfully performing the side-channel attack in the university's lab, Wouters notified the SpaceX product security team that he had achieved root-level access on the terminal, and said they offered him an easier way in: SSH access involving a Yubikey for authentication.
"But I decided that I was way too far down the rabbit hole and I didn't accept it," he said.
So he built a modchip, replacing the lab equipment with cheap off-the-shelf components, and used the homemade system to glitch the bootloader and obtain root access on the Starlink user terminal (UT).
After obtaining this superuser access, you can do pretty much anything to the UT, including deploying your own software or malware, fiddling with settings, and shutting down its communications. In Wouters' case, he used the security weakness to send a tweet through the rooted Starlink user terminal (UT) announcing his Black Hat talk.
A little more than a month after disclosing that gaps in the U.S. military’s electronic warfare toolkit are causing him to lose sleep, Army Undersecretary Gabe Camarillo said one of the service’s premier efforts to provide jamming and sensing capabilities shows promise.
The Army showcased its Multi-Function Electronic Warfare-Air Large pod this week in Aberdeen, Maryland. The service is building back its EW arsenal after decades focused on counterterrorism, confronting forces that were less technologically savvy. The targeting of communications and other networks seen daily in the war in Ukraine is adding to the sense of urgency, U.S. officials say.
EW is a fight over control of the electromagnetic spectrum, which militaries use for situational awareness, communications and weapons guidance. The contest is increasingly important as more and more-advanced technologies are deployed on the battlefield and troops try to minimize signatures to avoid detection.
“What concerned me, always, is that we’ve got to keep pace with the threat over time,” Camarillo told reporters Aug. 23, following a morning of briefings. “I’m really impressed with the MFEW program that the Army has, its different configurations and where it’s going.”
The self-contained pod, made by Lockheed Martin, was intended to be mounted to an MQ-1C Gray Eagle drone. Other platforms are now being explored. The Air Force has expressed interest in working it into an A-10 attack plane, and testing is anticipated with the High Accuracy Detection and Exploitation System, a jet tooled for intelligence, surveillance and reconnaissance.
As long as a power supply and an ethernet port are available, MFEW-AL is an option, officials said Tuesday.

Army demos aerial jammer amid push to catch up in electronic warfare
U.S. Army Undersecretary Gabe Camarillo said he was "really impressed with the MFEW program," its "different configurations and where it's going."

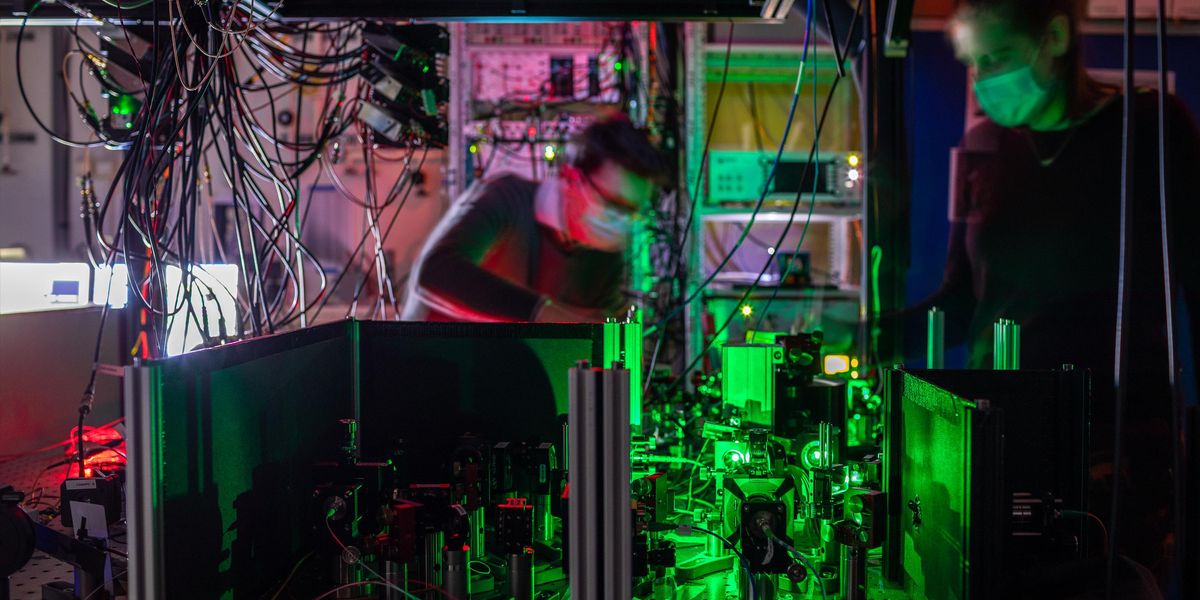
With AI systems getting smarter every day, one might wonder if they might someday evolve into a sentient Skynet-like system and try to take over the world. We’re not sure how close we are to such a situation, but we do know that if the robot apocalypse were to happen, we would want to stay close to [LordOfAllThings], who would likely be carrying the Black Beast. This scary-sounding machine is in essence a Raspberry Pi-based portable computer built inside an outdoor carrying case, with a wide range of unusual peripherals that make it the digital equivalent of a Swiss army knife. In other words, it’s a cyberdeck built for end times — and whatever comes after.

2022 Cyberdeck Contest: The Black Beast Will Help You Survive A Robot Apocalypse
With AI systems getting smarter every day, one might wonder if they might someday evolve into a sentient Skynet-like system and try to take over the world. We’re not sure how close we are to …
For example, an array of ESP32-based modules plus an SDR module allow you to intercept and analyze hostile robots’ communications, whether they’re using Bluetooth, WiFi, LoRaWAN, or anything in the 433 or 868 MHz ranges. An FM transmitter comes in handy for reaching out to fellow citizens who are trapped with nothing more than an analog radio receiver, while a suite of environmental sensors (including a Geiger counter) should help determine if Skynet has released any harmful substances to flush out those last few pesky humans. (Ed. note: No marigolds in the promised land and all that.)
If you manage to find a wired Ethernet connection somewhere, a built-in five-port gigabit router lets you set up a local network, obviously with a custom network analyzer to detect any unwanted intrusions. A storage compartment contains every kind of cable you could need, as well as useful gadgets like flashlights and, indeed, an actual Swiss army knife.
Naturally, the Black Beast can be run from any power source you might encounter, ranging from various AC mains voltages to the 12~48 V DC found in car batteries and solar panels. A built-in 12 Ah lead-acid battery gives it quite a bit of autonomy as well: a wide range of voltage and current monitors, as well as a clever power distribution system help you to manage power flows throughout the Black Beast.
The main user interfaces connected to the Pi are a 10.1″ full-HD monitor and a Logitech K400 keyboard/touch pad unit. All of the components are built into 3D-printed plug-in modules that neatly fit inside custom slots in the carrying case.
STL files and an extensive component list are available in case you’d like to build your own; apart from apocalyptic scenarios, such a machine would definitely be useful for things like maintenance and debugging of machinery out in the field.
The Black Beast
The "Black Beast" prototype is not only a heavy-duty Cyberdeck, but also an experimental sensor and hacking platform, which is still work in progress. It is my first Cyberdeck and I started building it in January 2022. The build process (which is still ongoing, especially for the SW part) was...
A shifting landscape of national security hazards coupled with constant technological advancement is pushing U.S. Army electronic warfare and situational awareness officials to focus on future flexibility.
“We have got to be able to have systems or capabilities that can adapt,” Mark Kitz, the Army’s program executive officer for intelligence, electronic warfare and sensors, said Aug. 30 during a media roundtable at the Open Innovation Lab.
The changing nature of theaters and threats means massive buys of rigid equipment can be risky, a factor that influences where money is spent and what research is conducted.
“Just think, the areas you’re going to operate in are going to look very different in spectrum and what you can do, whether it’s in Africa, if it’s in SOUTHCOM,” Kitz said, referencing U.S. Southern Command, which has an area of responsibility covering more than two-dozen countries. “Wherever you may be, it’s going to be just a very different environment. So we don’t want to buy the same thing to operate in all these different environments, right?”
“And that’s where I get to: I don’t think we’re going to get into the business of buying thousands of something,” he said. “I think we’re going to get into the business of buying years of something and evolving it over time.”

Army electronic warfare office seeks to adapt now for future threats
The U.S. Army is reinvigorating its networks, sensors, electronic warfare arsenal and related tools following decades of counterterrorism operations.
In the last three or four years, he said, “we’ve gone through three different versions of our dismounted gear. So we’re able to quickly pivot to the next technology and not necessarily go down long-term production of the same solution when the technology is iterating and the threat is iterating.”
The Army is reinvigorating its networks, sensors, EW arsenal and related tools following decades of counterterrorism operations — a period when troops engaged with forces sporting less-advanced gear and communications were less at risk.
The U.S. is now preparing for potential fights against China and Russia, two world powers that spend significantly on military science and technology. The targeting of networks and other battlefield systems seen in the Russia-Ukraine war is only adding to the sense of urgency.
“Jamming and spoofing are a real threat out there,” Maj. Matthew Szarzynski, an assistant project manager at PEO IEW&S, said. “As the threat kind of evolves, we need to kind of match that threat.”
Ukraine’s minister of defense, Oleksii Reznikov, in July described his embattled country as both a testing ground and a fount of information. U.S. defense officials say they are gleaning from the conflict key information about Russian weapons, tactics and capacity.
Satellite navigation and tracking via GPS has become a critical link in the world's rapidly growing logistics and freight carrying ecosystem. Companies use GPS to track trucks and keep them on time and their cargo secure.
Little wonder, then, that criminals are turning to cheap GPS jamming devices to ransack the cargo on roads and at sea, a problem that's getting worse but may be ameliorated with a new generation of safety technology designed to overcome threats from jamming.

GPS jammers are being used to hijack trucks and down drones: How to stop them
The problem of GPS jamming has spawned an array of anti-jamming solutions.
 www.zdnet.com
www.zdnet.com
In Mexico, jammers are used in some 85% of cargo truck thefts. Statistics are harder to come by in the United States, but there can be little doubt the devices are prevalent and widely used. Russia is currently availing itself of the technology to jam commercial planes in Ukraine.
As we've covered, the proliferating commercial drone sector is also prey to attack. Drones often rely on GPS for navigation as well as security tracking, making them especially vulnerable. Drones equipped with back-up methods still often rely on GPS for positioning, navigation, and stabilization, making jammers a way to take a drone down and potentially cause harm to life and property. During a light show in Hong Kong in 2018, a jamming device caused 46 drones to fall out of the sky, raising public awareness of the issue.

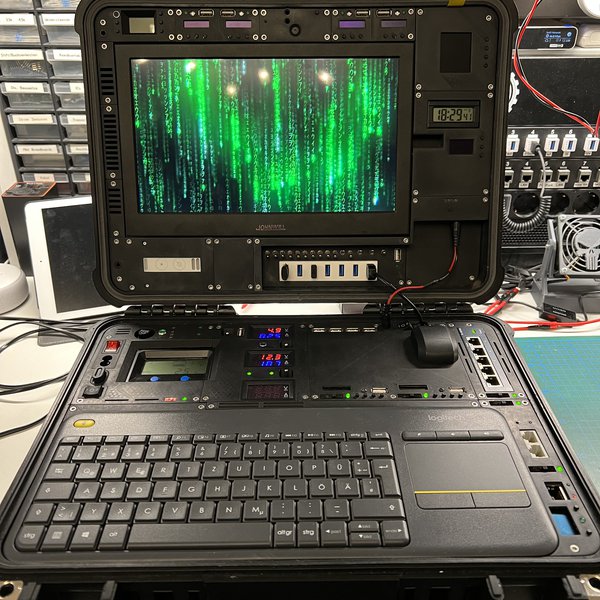
Feeling confined by the “traditional” cyberdeck form factor, [adam] decided to build something a little bigger with his Cyberpack VR. If you’ve ever dreamed of being a WiFi-equipped porcupine, then this is the cyberdeck you’ve been waiting for.
Craving the upgradability and utility of a desktop in a more portable format, [adam] took an old commuter backpack and squeezed in a Windows 11 PC, Raspberry Pi, multiple wifi networks, an ergonomic keyboard, a Quest VR headset, and enough antennas to attract the attention of the FCC. The abundance of network hardware is due to [adam]’s “new interest: a deeper understanding of wifi, and control of my own home network even if my teenage kids become hackers.”
The Quest is setup to run multiple virtual displays via Immersed, and you can relax on the couch while leaving the bag on the floor nearby with the extra long umbilical. One of the neat details of this build is repurposing the bag’s external helmet mount to attach the terminal unit when not in use. Other details we love are the toggle switches and really integrated look of the antenna connectors and USB ports. The way these elements are integrated into the bag makes it feel borderline organic – all the better for your cyborg chic.
For more WiFi backpacking goodness you may be interested in the Pwnton Pack. We’ve also covered other non-traditional cyberdecks including the Steampunk Cyberdeck and the Galdeano.

2022 Cyberdeck Contest: Cyberpack VR
Feeling confined by the “traditional” cyberdeck form factor, [adam] decided to build something a little bigger with his Cyberpack VR. If you’ve ever dreamed of being a WiFi-equipp…
CyberPack VR
Contains: A fat battery A windows 11 machine that serves a VR client enabling multiple private high resolution monitors A kali linux raspberry pi running Alfa wifi with MediaTek 7612U chipset A wifi pineapple A wired network Many wireless networks Lots of antennae Lots of fans A quest 2 An...
vonrehausen
Luutnantti
Venäläinen elektroninen sodankäynti webinaari 19.10.2022 klo 18:00-21:00
Viestikiltojen Liitto ja Elektronisen sodankäynnin kilta järjestävät yhteistyössä webinaarin otsikolla:
VENÄLÄINEN ELEKTRONINEN SODANKÄYNTI
googlella löytyy yhteystiedot
Viestikiltojen Liitto ja Elektronisen sodankäynnin kilta järjestävät yhteistyössä webinaarin otsikolla:
VENÄLÄINEN ELEKTRONINEN SODANKÄYNTI
googlella löytyy yhteystiedot
GPS häirintää havaittu murmanskissa:
Ukraina vitjassa olikin näistä valoilmiöistä. Taipuisin uskomaan että nämä tapahtumat liittyvät toisiinsa:
Ukraina vitjassa olikin näistä valoilmiöistä. Taipuisin uskomaan että nämä tapahtumat liittyvät toisiinsa:
Norppa
Eversti
Noita on nyt sen verran kattavasti nähty merkittävillä paikoilla, että jonkinlaista häirintää nuo on. En usko että lämpöjälkeä noilla voisi peittää saati SAR-satelliittia huijata, mutta kyllä noilla normi satelliittikuvat pilaa valaisemalla kostean yöilman vrt. sumukelissä joku ajaa pitkät päällä vastaan.GPS häirintää havaittu murmanskissa:
Ukraina vitjassa olikin näistä valoilmiöistä. Taipuisin uskomaan että nämä tapahtumat liittyvät toisiinsa:
GPS-häirintä varmaankin paikallista, jenkkien toimesta tuollaista kohdemaista tarkkuuden laskua ei kai saada aikaiseksi, vaikutusalue olisi paljon suurempi.
On the time scale of technological history, it really wasn't all that long ago that radio was -- well, boring. We're not talking about the relative entertainment value of the Jack Benny Show or listening to a Brooklyn Dodgers game, but about the fact that for the most part, radio was a one-dimensional medium: what you heard was pretty much all there was to a signal, and radio was rarely used for anything particularly hackable.
Not so today, of course, where anything electronic seems to have at least one radio stuffed into it, and the space around us is filled with a rich soup of fascinating RF signals. For hackers, this is where radio gets interesting -- listening in on those signals, exploring their nature, and figuring out how to put them to use are like red meat for us.
Hacking and reverse engineering opportunities abound in the RF realm, but can sometimes be a bit difficult. What's needed is a framework for pulling those signals out of the ether and putting them into some kind of context. Fortunately, there are plenty of tips and tricks in this space; we talked about one of them, FISSURE, not too long ago. The acronym -- "Frequency Independent SDR-Based Signal Understand and Reverse Engineering" -- about sums up what this framework is all about. But to bring it into further focus, we're lucky enough to have Chris Poore, a Senior Reverse Engineer at Assured Information Security, drop by the Hack Chat. We'll talk about RF reverse engineering in general and FISSURE in particular. Be sure to stop by with your RF hacking and reverse engineering questions and war stories!

Designed and built in the UAE, V-Protect is fully self-contained, with the option of an external power source for “on-the-pause” operation and built-in shock absorbers to protect the system during high-speed or rough-terrain driving.
V-Protect is an advanced mobile active and reactive high-power jammer system aimed at helping block common terrestrial RF signal technologies as well as portable Satcom equipment, spanning radio, walkie-talkie, mobile and Wi-Fi frequencies. Boasting a counter-improvised explosive device (C-IED) and counter-drone measures, the user-friendly model is to be installed in a standard SUV (Sport Utility Vehicle) that was showcased at IDEX 2021 and offers automatic operability by utilizing 16 channels and high emitting power amplifiers to provide support in enhancing protection range and combatting various threats across the frequency domain. A V-Protect-equipped vehicle is intended to be deployed at the front and at the back of a convoy, so ensuring the neutralization of any attempt to trigger IEDs by any kind of wave.
SIGN4L is part of the Electronic Warfare & Intelligence cluster at EDGE, an advanced technology group that ranks among the top 25 military suppliers in the world. The new V-Protect radio frequency (RF) communication jamming system was designed and developed by SIGN4L, a subdivision of EDGE to counter Remote controlled improvised Explosive Devices, roadside bombs, and other threats controlled by mobile phones or other radio signals.
Mounted on a vehicle, the V-Protect can be used to conduct counter-terrorism operations or to protect military convoys and VIPs' transport. The vehicle located at the front and a the end of the convoy can provide full 360° protection using the onboard V-Protect solution for radio signal jamming.
SIGN4L from UAE showcases V-Protect radio frequency communication jamming system at ISNR 2022 | Defense News October 2022 Global Security army industry | Defense Security global news industry army year 2022 | Archive News year
SIGN4L from UAE showcases V-Protect radio frequency communication jamming system at ISNR 2022
apumekaanikko
Majuri
Ketju EMP:istä ja sen vaikutuksesta eri etäisyyksiltä.
Tekijäjä Edward Geist - @sovietologist
Policy Researcher - @RANDCorporation.
Work on nuclear weapons and warfare, Russia, and artificial intelligence.
 threadreaderapp.com
threadreaderapp.com
Tekijäjä Edward Geist - @sovietologist
Policy Researcher - @RANDCorporation.
Work on nuclear weapons and warfare, Russia, and artificial intelligence.
Thread by @sovietologist on Thread Reader App
@sovietologist: Folks are asking about the electromagnetic pulse (EMP) effects from the battlefield use of nuclear weapons. TL;DR-if you're close enough to a near-surface nuclear burst to worry about its EMP, you're...…


